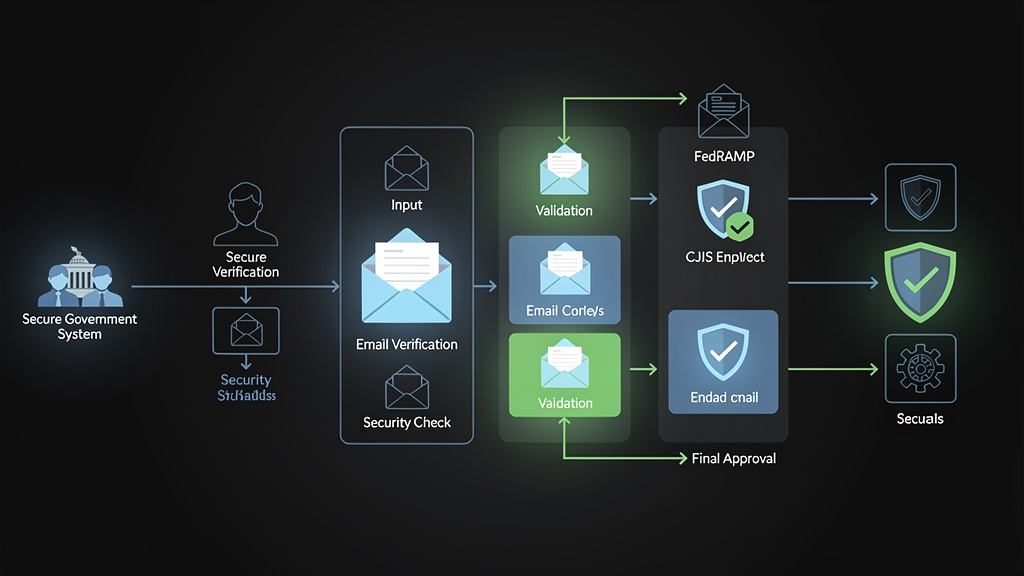
Email Verification for Government: Meeting FedRAMP and CJIS Standards
Government agencies deploying email verification systems face a uniquely unforgiving compliance landscape — one where a misconfigured DNS record or an improperly handled SMTP response isn't just a deliverability problem, it's a potential federal audit finding. When your email infrastructure touches citizen data, law enforcement records, or federal employee communications, the stakes of getting verification wrong extend far beyond bounce rates and sender reputation scores.
Why Government Email Verification Is a Different Beast Entirely
Most organizations treat email verification as a deliverability optimization problem. Government agencies cannot afford that luxury. For federal systems operating under FedRAMP authorization and state and local law enforcement systems governed by CJIS Security Policy, email verification sits at the intersection of operational efficiency, data sovereignty, and federal compliance mandates that carry real legal consequences.
Consider the scale of the problem. According to Validity's 2023 Sender Intelligence Report, the average email list decays at a rate of approximately 22.5% per year — meaning nearly one in four email addresses in a government database becomes invalid within twelve months. For a federal agency managing communications with millions of citizens, contractors, and inter-agency partners, that decay rate translates directly into failed notifications for benefit disbursements, missed security alerts, and undeliverable emergency communications.
The consequences aren't abstract. The Social Security Administration sends tens of millions of benefit-related emails annually. The IRS relies on email for taxpayer notifications. FEMA coordinates disaster response communications through email channels. When addresses go bad and email verification systems aren't compliant with federal security frameworks, agencies face a compounding problem: they can't clean their lists using just any third-party service, because doing so might violate the very compliance frameworks designed to protect the data they're handling.
The Regulatory Trifecta Governing Federal Email Infrastructure
Federal email systems must navigate three overlapping compliance frameworks simultaneously:
- FedRAMP (Federal Risk and Authorization Management Program) — governs cloud services used by federal agencies, requiring NIST SP 800-53 security controls
- CJIS (Criminal Justice Information Services) Security Policy — applies to any system that touches criminal justice information, including law enforcement email systems
- FISMA (Federal Information Security Modernization Act) — the overarching federal cybersecurity law that FedRAMP operationalizes for cloud services
Understanding how email verification intersects with each framework is the foundation for building a compliant system that actually works.
Understanding FedRAMP Authorization and What It Means for Email Verification APIs
FedRAMP was established in 2011 to provide a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. When a government agency wants to use a cloud-based email verification service — including API-based solutions — that service must either hold a FedRAMP authorization or the agency must conduct its own assessment under FISMA.
FedRAMP Impact Levels and Email Verification
FedRAMP defines three impact levels based on the sensitivity of the data being processed:
Low Impact applies to systems where the loss of confidentiality, integrity, or availability would have limited adverse effects. A public-facing email newsletter signup form might fall here.
Moderate Impact covers the majority of federal systems — those handling Controlled Unclassified Information (CUI). Most citizen-facing government portals, benefits systems, and inter-agency communication platforms operate at this level. FedRAMP Moderate requires compliance with 325 security controls from NIST SP 800-53.
High Impact applies to systems where a breach would have severe or catastrophic consequences — think law enforcement databases, national security systems, or financial regulatory infrastructure. FedRAMP High requires 421 controls.
For email verification specifically, the critical FedRAMP controls that come into play include:
- AC-3 (Access Enforcement) — controlling who can query email verification endpoints
- AU-2 (Event Logging) — maintaining audit trails of all verification requests
- SC-8 (Transmission Confidentiality and Integrity) — requiring encryption for data in transit
- SA-9 (External Information System Services) — governing the use of third-party API services
- RA-5 (Vulnerability Scanning) — ensuring the verification infrastructure itself is regularly assessed
The FedRAMP Marketplace and Compliant Service Selection
The FedRAMP Marketplace lists authorized cloud services. As of 2024, agencies are increasingly requiring that any API service processing government email addresses — even indirectly — either holds FedRAMP authorization or can demonstrate equivalent controls through a System Security Plan (SSP).
This creates a practical challenge: many commercial email verification APIs are excellent at what they do technically, but haven't pursued FedRAMP authorization because the process is expensive (typically $250,000 to $500,000 for initial authorization) and time-consuming (12 to 18 months on average). Agencies working with non-authorized services must document their risk acceptance and implement compensating controls.
CJIS Security Policy: The Strictest Email Compliance Framework in U.S. Law Enforcement
The FBI's Criminal Justice Information Services (CJIS) Security Policy is arguably the most demanding data security framework applied to state and local government systems in the United States. Any agency that accesses the National Crime Information Center (NCIC), the National Instant Criminal Background Check System (NICS), or other FBI-managed criminal justice databases must comply with CJIS — and that compliance extends to every system that touches the same network infrastructure.
Why Email Verification Touches CJIS Systems
Law enforcement agencies use email extensively for:
- Inter-agency coordination on active investigations
- Notifications to officers about warrant status and database updates
- Communications between prosecutors, public defenders, and courts
- Citizen notifications about case status and hearings
- Personnel communications within agencies that have CJIS access
When an agency's email system sits on the same network as CJIS-connected systems — which is common in smaller departments — any cloud service that processes email addresses from that environment potentially falls under CJIS scrutiny.
Key CJIS Requirements Affecting Email Verification
Section 5.5 — Access Control: CJIS requires that access to criminal justice information be limited to authorized personnel with a documented need to know. For email verification systems, this means API keys and verification logs must be access-controlled and auditable.
Section 5.6 — Identification and Authentication: Multi-factor authentication is mandatory for any remote access to CJIS-compliant systems. Email verification API calls originating from law enforcement systems must come from authenticated, authorized sources.
Section 5.8 — Audit and Accountability: Every access to CJI must be logged with sufficient detail to reconstruct events. Email verification logs — including what addresses were verified, when, by whom, and what the result was — become part of the audit trail.
Section 5.10 — Systems and Communications Protection: Data in transit must be encrypted using FIPS 140-2 validated cryptographic modules. This means TLS 1.2 minimum (TLS 1.3 preferred) for all API communications, and the TLS implementation must use FIPS-validated cipher suites.
Section 5.12 — Personnel Security: Any vendor whose personnel might have access to CJI — including cloud service providers — must conduct FBI fingerprint-based background checks on those personnel.
This last requirement is often the deal-breaker for commercial email verification services. Most SaaS providers cannot practically subject their entire engineering and operations staff to FBI background checks, which is why many law enforcement agencies end up building on-premises or government-cloud-based email verification solutions.
The Technical Architecture of Government-Compliant Email Verification
Building an email verification system that satisfies both FedRAMP and CJIS requirements demands a specific technical architecture. Let's walk through the components and the technical standards that govern each.
SMTP-Level Verification and RFC Compliance
Email verification at the SMTP level involves a sequence of protocol interactions defined in RFC 5321 (Simple Mail Transfer Protocol). A compliant verification system must handle the full range of SMTP response codes and interpret them correctly.
The verification sequence works as follows:
- DNS MX record lookup to identify mail servers for the target domain
- TCP connection to the mail server on port 25 (or 587 for submission)
- SMTP handshake (EHLO/HELO)
- MAIL FROM command with a probe address
- RCPT TO command with the target address
- Interpretation of the server's response code
- QUIT command to close the connection gracefully
The response codes, defined in RFC 3463 (Enhanced Mail System Status Codes), tell the verification system what happened:
2xx codes indicate success:
- 250 — Requested mail action okay, completed. The address exists and the server accepted it.
- 251 — User not local; will forward. The address may be valid but is handled elsewhere.
4xx codes indicate temporary failures:
- 421 — Service not available, closing transmission channel. The server is temporarily unavailable; don't mark the address as invalid.
- 450 — Requested mail action not taken: mailbox unavailable. Temporary condition — the mailbox exists but can't receive mail right now.
- 451 — Requested action aborted: local error in processing. Server-side issue; try again later.
- 452 — Requested action not taken: insufficient system storage. Temporary; the mailbox is full.
5xx codes indicate permanent failures:
- 550 — Requested action not taken: mailbox unavailable. The address doesn't exist or has been disabled. This is the definitive "invalid address" response.
- 551 — User not local; please try another path. The server is rejecting relay attempts.
- 552 — Requested mail action aborted: exceeded storage allocation. The mailbox exists but is permanently over quota.
- 553 — Requested action not taken: mailbox name not allowed. Syntax or policy issue with the address.
For government systems, the distinction between 4xx and 5xx responses is critical. Incorrectly treating a 450 (temporary unavailability) as a 550 (permanent failure) and removing a valid email address from a government database could mean a citizen misses a critical benefit notification. Verification systems must implement proper retry logic for all 4xx responses.
DNS Record Validation for Government Domains
Government email domains use specific DNS configurations that verification systems must understand. The .gov TLD is managed by CISA (Cybersecurity and Infrastructure Security Agency) and has strict requirements for all registrants.
A properly configured government email domain will have:
MX Records pointing to authorized mail servers:
agency.gov. IN MX 10 mail1.agency.gov.
agency.gov. IN MX 20 mail2.agency.gov.
SPF Record (defined in RFC 7208) specifying authorized sending sources:
agency.gov. IN TXT "v=spf1 ip4:198.51.100.0/24 ip4:203.0.113.0/24 include:mail.agency.gov -all"
The -all qualifier (hard fail) is mandatory for .gov domains under CISA's Binding Operational Directive 18-01, which requires DMARC enforcement at the p=reject level.
DKIM Record (defined in RFC 6376) for cryptographic signing:
selector1._domainkey.agency.gov. IN TXT "v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQC..."
DMARC Record (defined in RFC 7489) enforcing authentication:
_dmarc.agency.gov. IN TXT "v=DMARC1; p=reject; rua=mailto:[email protected]; ruf=mailto:[email protected]; pct=100; adkim=s; aspf=s"
Note the adkim=s and aspf=s settings, which enforce strict alignment mode — a CISA requirement for .gov domains. Verification systems must check these records as part of domain-level validation.
Handling Catch-All Domains in Government Infrastructure
Many government agencies configure their mail servers as catch-all servers, meaning the server accepts mail for any address at the domain regardless of whether the specific mailbox exists. This is common in agencies where mail routing is handled internally after acceptance.
A catch-all server will return 250 for RCPT TO: <[email protected]> just as readily as for a real address. Standard SMTP verification fails in this scenario.
Handling catch-all detection requires:
- Sending a RCPT TO command with a provably nonexistent address (e.g., a randomly generated string like
[email protected]) - If the server returns
250for this address, flag the domain as catch-all - Fall back to alternative verification methods: DNS record analysis, syntax validation, domain reputation scoring, and historical bounce data
For government systems, this is especially important because many .gov and .mil domains are configured as catch-alls for operational reasons.
Implementing Government-Compliant Email Verification: A Production Guide
Here's where theory meets implementation. Building a government-compliant email verification integration requires attention to security, auditability, and graceful error handling that goes well beyond a basic API call.
Setting Up a FedRAMP-Aware Verification Pipeline
The following Python implementation demonstrates a production-ready email verification integration with MailValid's API, incorporating the security and logging requirements appropriate for government contexts:
import requests
import logging
import hashlib
import json
import time
from datetime import datetime, timezone
from typing import Optional, Dict, Any
from dataclasses import dataclass, asdict
# Configure structured logging for audit trail compliance
logging.basicConfig(
level=logging.INFO,
format='%(asctime)s - %(name)s - %(levelname)s - %(message)s'
)
logger = logging.getLogger('gov_email_verification')
@dataclass
class VerificationAuditRecord:
"""
Immutable audit record for CJIS/FedRAMP compliance.
Email is hashed to avoid storing PII in logs.
"""
timestamp_utc: str
email_hash: str # SHA-256 hash of email for audit without PII exposure
domain: str
verification_result: str
smtp_response_code: Optional[int]
is_catch_all: bool
request_id: str
processing_time_ms: float
compliance_flags: Dict[str, bool]
class GovernmentEmailVerifier:
"""
Production email verification client for government systems.
Implements FedRAMP Moderate and CJIS-compatible security controls.
"""
BASE_URL = "https://mailvalid.io/api/v1/verify"
MAX_RETRIES = 3
RETRY_BACKOFF_BASE = 2 # Exponential backoff base in seconds
TIMEOUT_SECONDS = 30
def __init__(self, api_key: str, agency_id: str, system_id: str):
"""
Initialize verifier with government system identifiers for audit trail.
Args:
api_key: MailValid API key (store in secrets manager, never hardcode)
agency_id: Agency identifier for audit logging (e.g., "DOJ-FBI-CJIS")
system_id: System identifier for audit logging (e.g., "NCIC-EMAIL-SVC")
"""
if not api_key.startswith("mv_live_"):
raise ValueError("Production API key required for government systems")
self.api_key = api_key
self.agency_id = agency_id
self.system_id = system_id
# Configure session with government-appropriate TLS settings
self.session = requests.Session()
self.session.headers.update({
"X-API-Key": self.api_key,
"Content-Type": "application/json",
"User-Agent": f"GovEmailVerifier/1.0 ({agency_id}/{system_id})",
"X-Agency-ID": agency_id,
"X-System-ID": system_id
})
# Force TLS 1.2+ for FIPS compliance (CJIS Section 5.10)
# In production, configure adapter with FIPS-validated cipher suites
self.session.verify = True # Always verify SSL certificates
def _hash_email_for_audit(self, email: str) -> str:
"""Hash email address for audit logging without storing PII."""
return hashlib.sha256(email.lower().encode('utf-8')).hexdigest()
def _generate_request_id(self, email: str) -> str:
"""Generate deterministic request ID for correlation."""
timestamp = str(time.time_ns())
return hashlib.sha256(f"{email}{timestamp}{self.system_id}".encode()).hexdigest()[:16]
def _assess_compliance_flags(self, result: Dict[str, Any]) -> Dict[str, bool]:
"""
Assess compliance-relevant flags from verification result.
Returns dict of flags relevant to FedRAMP/CJIS risk assessment.
"""
return {
"spf_valid": result.get("spf_valid", False),
"dkim_valid": result.get("dkim_valid", False),
"dmarc_enforced": result.get("dmarc_policy") in ["quarantine", "reject"],
"is_disposable": result.get("is_disposable", False),
"is_role_account": result.get("is_role_account", False),
"is_government_domain": result.get("domain", "").endswith((".gov", ".mil", ".fed.us")),
"tls_supported": result.get("smtp_tls_supported", False),
"catch_all_domain": result.get("is_catch_all", False)
}
def verify_email(self, email: str) -> Dict[str, Any]:
"""
Verify a single email address with full audit logging.
Implements exponential backoff for 4xx SMTP responses (RFC 5321 compliance)
and full audit trail generation for FedRAMP AU-2 control compliance.
Args:
email: Email address to verify
Returns:
Dict containing verification result and audit record
Raises:
ValueError: For invalid email format
requests.exceptions.SSLError: If TLS validation fails
RuntimeError: If max retries exceeded
"""
start_time = time.monotonic()
request_id = self._generate_request_id(email)
email_hash = self._hash_email_for_audit(email)
# Basic format validation before making API call
if not email or '@' not in email or len(email) > 254:
raise ValueError(f"Invalid email format: request_id={request_id}")
domain = email.split('@')[1].lower()
logger.info(
"Email verification initiated",
extra={
"request_id": request_id,
"email_hash": email_hash,
"domain": domain,
"agency_id": self.agency_id,
"system_id": self.system_id
}
)
last_exception = None
for attempt in range(self.MAX_RETRIES):
try:
response = requests.post(
self.BASE_URL,
headers={"X-API-Key": "mv_live_key"},
json={"email": email},
timeout=self.TIMEOUT_SECONDS
)
result = response.json()
# Handle rate limiting with exponential backoff
if response.status_code == 429:
retry_after = int(response.headers.get('Retry-After',
self.RETRY_BACKOFF_BASE ** attempt))
logger.warning(
f"Rate limited, backing off {retry_after}s",
extra={"request_id": request_id, "attempt": attempt}
)
time.sleep(retry_after)
continue
response.raise_for_status()
# Calculate processing time for audit record
processing_time_ms = (time.monotonic() - start_time) * 1000
# Build compliance assessment
compliance_flags = self._assess_compliance_flags(result)
# Generate immutable audit record (required for CJIS Section 5.8)
audit_record = VerificationAuditRecord(
timestamp_utc=datetime.now(timezone.utc).isoformat(),
email_hash=email_hash,
domain=domain,
verification_result=result.get("status", "unknown"),
smtp_response_code=result.get("smtp_response_code"),
is_catch_all=result.get("is_catch_all", False),
request_id=request_id,
processing_time_ms=round(processing_time_ms, 2),
compliance_flags=compliance_flags
)
# Log audit record (in production, write to immutable audit log store)
logger.info(
"Email verification completed",
extra={"audit_record": asdict(audit_record)}
)
# Flag high-risk results for human review
if compliance_flags.get("is_disposable") or not compliance_flags.get("dmarc_enforced"):
logger.warning(
"High-risk email detected — flagged for review",
extra={
"request_id": request_id,
"risk_flags": compliance_flags
}
)
return {
"verification_result": result,
"audit_record": asdict(audit_record),
"request_id": request_id
}
except requests.exceptions.SSLError as e:
# SSL errors must never be silently ignored in government systems
logger.critical(
f"TLS validation failure — potential security incident: {str(e)}",
extra={"request_id": request_id}
)
raise # Do not retry SSL errors; escalate immediately
except requests.exceptions.Timeout:
logger.warning(
f"Verification timeout on attempt {attempt + 1}",
extra={"request_id": request_id}
)
last_exception = TimeoutError(f"Verification timed out after {self.TIMEOUT_SECONDS}s")
except requests.exceptions.RequestException as e:
logger.error(
f"Verification request failed on attempt {attempt + 1}: {str(e)}",
extra={"request_id": request_id}
)
last_exception = e
# Exponential backoff before retry
if attempt < self.MAX_RETRIES - 1:
backoff = self.RETRY_BACKOFF_BASE ** attempt
time.sleep(backoff)
raise RuntimeError(
f"Email verification failed after {self.MAX_RETRIES} attempts. "
f"request_id={request_id}"
) from last_exception
# Example usage for a government system
if __name__ == "__main__":
import os
# API key must come from a secrets manager, never from code or environment variables
# in production. Using env var here for demonstration only.
api_key = os.environ.get("MAILVALID_API_KEY")
verifier = GovernmentEmailVerifier(
api_key=api_key,
agency_id="USDA-FNS", # USDA Food and Nutrition Service
system_id="SNAP-PORTAL-EMAIL-SVC"
)
result = verifier.verify_email("[email protected]")
print(json.dumps(result, indent=2))
This implementation satisfies several critical compliance requirements simultaneously: it hashes email addresses before logging them (protecting PII), generates immutable audit records (satisfying CJIS Section 5.8), enforces TLS validation (CJIS Section 5.10), and implements proper retry logic that respects RFC 5321's guidance on handling temporary SMTP failures.
Common Mistakes Government Agencies Make with Email Verification
Understanding the failure modes is as important as understanding the correct approach. Government agencies consistently make a predictable set of mistakes when implementing email verification systems.
Mistake 1: Treating All Invalid Responses as Permanent Failures
The single most damaging mistake is removing email addresses from government databases based on temporary SMTP failures. When a mail server returns 421 (service temporarily unavailable) or 450 (mailbox temporarily unavailable), those are transient conditions. A citizen's email provider might be experiencing a brief outage. Removing that address permanently means the citizen may never receive their benefit notification, jury summons, or emergency alert.
Government systems must implement a quarantine-before-removal policy: addresses that return 4xx codes should be quarantined for a retry period (typically 72 hours across multiple retry attempts) before being flagged for removal. Only consistent 5xx responses across multiple verification attempts over time should trigger permanent removal.
Mistake 2: Storing Unencrypted Email Addresses in Verification Logs
Audit logging is mandatory under both FedRAMP and CJIS — but logging raw email addresses creates a secondary data exposure risk. Email addresses are PII under the Privacy Act of 1974 and must be handled accordingly. The correct approach, demonstrated in the code above, is to log a SHA-256 hash of the email address. This allows audit trail correlation (you can verify that a specific address was checked at a specific time) without exposing the actual PII in log files.
Mistake 3: Using Non-FIPS-Validated Cryptography
CJIS Section 5.10 explicitly requires FIPS 140-2 validated cryptographic modules for data in transit. Many organizations assume that "using HTTPS" satisfies this requirement — it does not, unless the TLS implementation uses FIPS-validated cipher suites. In Python, this means using a version of OpenSSL compiled with FIPS mode enabled. In government deployments, this typically means running on a FIPS-validated operating system image (RHEL with FIPS mode, for example) rather than relying on the application layer to enforce FIPS compliance.
Mistake 4: Failing to Validate the Verification Service's Own Security Posture
Agencies often focus on their own compliance posture while neglecting to assess the security posture of the email verification service they're using. Under FedRAMP control SA-9 (External Information System Services), agencies must document the security controls of external services and ensure they meet the agency's security requirements. This means obtaining SOC 2 Type II reports, reviewing the service's data processing agreements, and confirming data residency (email addresses must not be processed on infrastructure outside the United States for most federal systems).
Mistake 5: Not Accounting for .gov Domain-Specific Behaviors
The .gov TLD has unique characteristics that commercial email verification services may not handle correctly. CISA's BOD 18-01 requires all .gov domains to implement DMARC at p=reject, which means verification probes from poorly configured verification systems may be rejected or trigger security alerts at the target agency. Government email verification systems must use properly configured probe addresses and handle the strict DMARC enforcement common on .gov domains without generating false negatives.
Mistake 6: Ignoring Role-Based Address Policies
Government agencies frequently use role-based email addresses ([email protected], [email protected], [email protected]). RFC 2142 defines a standard set of role-based mailbox names that should exist at every domain. However, government systems should not send personalized citizen communications to role-based addresses — these are operational mailboxes, not individual recipients. Email verification systems must flag role-based addresses and route them through appropriate review rather than treating them as standard individual addresses.
Comparing Deployment Models for Government Email Verification
Government agencies have three primary deployment models for email verification, each with distinct compliance implications.
Model 1: On-Premises Verification Infrastructure
Agencies build and operate their own SMTP verification infrastructure within their data centers or government-owned cloud environments (GovCloud). This model offers maximum control and eliminates third-party data sharing concerns, but requires significant engineering investment.
Pros: - Complete data sovereignty — email addresses never leave agency infrastructure - No third-party compliance assessment required - Full control over logging, retention, and audit trail format
Cons: - High maintenance burden — SMTP landscape changes constantly (IP reputation, rate limiting, new anti-abuse measures) - Difficult to maintain comprehensive catch-all domain detection without large-scale data - Requires dedicated engineering resources for ongoing maintenance - May struggle with accuracy compared to services with broad data networks
Model 2: FedRAMP-Authorized SaaS Verification
Using a cloud-based email verification API that holds FedRAMP authorization. This is the preferred model for most federal civilian agencies.
Pros: - Compliance burden shared with the authorized service provider - Access to continuously updated verification data and algorithms - Scalable without infrastructure investment - Provider handles SMTP rate limiting and IP reputation management
Cons: - Limited pool of FedRAMP-authorized email verification providers - Ongoing monitoring and compliance documentation required - Data processing agreements must be carefully reviewed - Potential latency from government network to provider infrastructure
Model 3: Government Community Cloud with Compliant API
Deploying a commercial email verification API within a FedRAMP-authorized government community cloud environment (AWS GovCloud, Azure Government, Google Cloud for Government), with the API service operating within the agency's FedRAMP authorization boundary.
Pros: - Leverages existing FedRAMP-authorized infrastructure - Agency maintains control over data residency - Can use commercial API services without requiring those services to independently hold FedRAMP authorization - Inherits security controls from the cloud environment's authorization
Cons: - More complex architecture requiring API proxy or gateway configuration - Performance overhead from government cloud routing - Requires careful architecture review to ensure the API service operates within the authorization boundary
According to a 2023 Gartner analysis of federal cloud adoption, 67% of federal agencies are now using or planning to use government community cloud environments for sensitive workloads — making Model 3 increasingly attractive for email verification deployments.
Best Practices for Government Email Verification Programs
Synthesizing the compliance requirements, technical constraints, and operational realities, here are the definitive best practices for government email verification programs.
Establish a Verification Frequency Policy
Government email databases should be verified on a structured schedule, not just at point of collection. Recommended frequencies:
- At collection: Verify every new email address before it enters the authoritative database
- Quarterly: Re-verify all active addresses in the database
- Event-triggered: Re-verify any address that generates a bounce or complaint signal
- Pre-campaign: Verify all addresses before any bulk communication campaign
Implement a Risk-Stratified Response to Verification Results
Not all verification outcomes warrant the same response. A risk-stratified approach:
Tier 1 — Valid and authenticated (SPF/DKIM/DMARC all pass): Use normally, no action required.
Tier 2 — Valid but authentication gaps: Use for communications but flag for domain administrator outreach. Common for smaller local government domains that haven't fully implemented email authentication.
Tier 3 — Catch-all domain, individual validity unknown: Use with caution, monitor bounce rates closely, implement preference confirmation workflow.
Tier 4 — Temporary failure (4xx SMTP): Quarantine for 72 hours, retry three times, escalate to Tier 5 if persistent.
Tier 5 — Permanent failure (5xx SMTP): Remove from active communications, retain record with verification timestamp for audit purposes, initiate alternative contact workflow if available.
Maintain Verification Records for Audit Purposes
Under both FedRAMP and CJIS, audit records must be retained for a minimum period (typically three years under NIST SP 800-53 AU-11). Verification records should include:
- Timestamp of verification (UTC)
- Hashed email address (not plaintext)
- Domain verified
- Verification result and SMTP response code
- Verification method used (SMTP, DNS-only, catch-all detection)
- System and user that initiated the verification
Coordinate with Agency ISSO and Legal Counsel
Email verification in government contexts is not purely a technical decision. The Information System Security Officer (ISSO) must be involved in selecting and authorizing verification tools, and legal counsel should review data processing agreements with any third-party verification service to ensure compliance with the Privacy Act, the E-Government Act, and any agency-specific data governance policies.
Test Verification Systems Against .gov and .mil Domains Specifically
Commercial email verification services are optimized for commercial email domains. Government systems should specifically test verification accuracy against .gov and .mil domains, which have unique characteristics including strict DMARC enforcement, catch-all configurations, and non-standard MX record configurations. Maintain a test corpus of known-valid and known-invalid .gov addresses to benchmark verification accuracy.
The Future of Government Email Verification: Emerging Standards and Requirements
The compliance landscape for government email verification is not static. Several emerging developments will shape requirements over the next two to five years.
CISA's Secure Cloud Business Applications (SCuBA) Initiative
CISA's SCuBA project is developing binding operational directives for cloud business applications used by federal agencies, including email systems. The SCuBA Google Workspace and Microsoft 365 baselines include specific requirements for email authentication and verification that go beyond existing BOD 18-01 requirements. Agencies using these platforms for citizen communications should monitor SCuBA guidance closely.
Zero Trust Architecture and Email Verification
The Biden Administration's Executive Order 14028 on Improving the Nation's Cybersecurity mandated zero trust architecture adoption across federal agencies. In a zero trust model, email addresses are identity attributes that must be continuously verified — not just validated at onboarding. This shifts email verification from a periodic hygiene activity to a continuous authentication signal, requiring real-time verification API integrations rather than batch processing.
Enhanced DMARC Enforcement Across Government Domains
CISA is progressively tightening DMARC requirements. Currently, BOD 18-01 requires p=reject for all .gov domains. As this enforcement matures, email verification systems will need to more accurately assess DMARC alignment for inbound emails from government domains, not just validate outbound sending configurations.
AI-Assisted Verification for Catch-All Domains
The catch-all domain problem — which disproportionately affects government verification — is increasingly being addressed through machine learning models trained on historical bounce data, engagement signals, and domain behavior patterns. Next-generation verification services will move beyond pure SMTP probe-based verification to probabilistic validity scoring that accounts for domain-specific behavioral patterns.
Conclusion: Government Email Verification Demands a Different Standard
Government email verification isn't a feature — it's a compliance obligation with direct consequences for citizen services, law enforcement operations, and national security. Meeting FedRAMP and CJIS standards requires understanding not just the technical mechanics of SMTP verification and DNS authentication, but the full regulatory context that governs how verification systems are built, deployed, audited, and maintained.
The technical foundations — RFC 5321 SMTP compliance, RFC 7208 SPF validation, RFC 6376 DKIM verification, RFC 7489 DMARC enforcement — are necessary but not sufficient. Government agencies must layer compliance controls on top of technical accuracy: FIPS-validated cryptography, immutable audit logging, PII-protective data handling, third-party vendor assessment, and risk-stratified response policies.
The cost of getting this wrong is measured not in bounce rates and sender reputation scores, but in failed citizen notifications, audit findings, and potentially compromised law enforcement operations. Government agencies that treat email verification as a first-class compliance requirement — not an afterthought — build communication infrastructure that serves citizens reliably while satisfying the rigorous demands of federal oversight.
For agencies evaluating government email verification solutions, the questions to ask are: Does this service meet FedRAMP authorization requirements? Can it satisfy CJIS data handling requirements? Does it produce audit-ready logs? Does it correctly handle the unique characteristics of .gov and .mil domains? The answers to those questions separate compliant, production-ready verification systems from solutions that create more compliance risk than they eliminate.
[!TIP]
Verify with Confidence Using MailValid MailValid provides enterprise-grade email verification built for organizations that can't afford to get it wrong. Our API delivers real-time SMTP verification, comprehensive DNS authentication checking (SPF, DKIM, DMARC), catch-all domain detection, and role-account identification — all over TLS 1.3 with detailed response logging. Whether you're building a FedRAMP-compliant citizen portal, integrating verification into a law enforcement communication system, or simply need production-ready email validation with the audit trail your compliance team requires, MailValid's API is designed for the challenge. Start verifying with MailValid today at mailvalid.io — explore our documentation, review our security posture, and request a compliance consultation with our solutions team. Your first 1,000 verifications are free.
MailValid Team
Email verification experts
Join developers who verify smarter
Stop letting bad emails hurt your deliverability
100 free credits. $0.001/email after. Credits never expire. No credit card required.