Lending platforms that skip rigorous email verification are handing fraudsters a free pass — and regulators are taking notice. In an industry where a single synthetic identity can cost a lender $15,000 or more in losses, the email address sitting at the top of every loan application is either your first line of defense or your first vulnerability.
Why Email Verification Is a KYC Imperative for Lending Platforms
The lending industry has a fraud problem that email verification can directly address, yet most platforms treat the email field as a simple text input with a regex check. That approach worked in 2005. Today, it's negligence.
According to LexisNexis Risk Solutions' 2023 True Cost of Fraud Study, financial services firms lose $4.36 for every dollar of fraud — a figure that has climbed 19% since 2019. The same study found that digital lending channels experience the highest fraud concentration, with mobile and online applications representing over 60% of all fraudulent loan submissions. Meanwhile, TransUnion's 2023 State of Omnichannel Fraud Report identified synthetic identity fraud as the fastest-growing financial crime in North America, costing lenders an estimated $2.42 billion annually.
What connects synthetic identities, bust-out fraud, and loan stacking schemes? They all rely on fabricated or manipulated digital identities — and the email address is the easiest identity component to fake. A fraudster can spin up a disposable email address in under 30 seconds. Without lending email verification at the infrastructure level, your KYC process has a gaping hole at its very first touchpoint.
This post is a technical and compliance deep-dive for engineering teams, fraud analysts, and compliance officers at fintech companies and lending platforms. We'll cover the SMTP-level mechanics of email verification, how it maps to KYC compliance frameworks, production-ready implementation patterns, and how fintech fraud prevention strategies can be built around a single, well-integrated API call.
The Anatomy of Lending Fraud and the Email Address's Role
Before diving into technical solutions, it's worth mapping exactly how email addresses are weaponized in lending fraud. This isn't abstract — understanding the attack vectors is essential for designing verification logic that actually stops fraud rather than just checking a compliance box.
Synthetic Identity Fraud and Disposable Emails
Synthetic identity fraud involves combining real and fabricated personally identifiable information (PII) to create a new identity that doesn't correspond to a real person. Fraudsters building synthetic identities need email addresses that:
- Accept incoming mail (to receive OTPs and loan documents)
- Don't trace back to a real person
- Can be abandoned the moment the fraud is complete
Disposable email providers — services like Mailinator, Guerrilla Mail, 10MinuteMail, and hundreds of others — are purpose-built for exactly this use case. According to Validity's 2023 Email Deliverability Report, disposable and temporary email domains account for approximately 8.4% of all email addresses collected by financial services companies through online forms. For a lending platform processing 10,000 applications per month, that's potentially 840 fraudulent or unverifiable applicants slipping through.
Loan Stacking and Email Permutations
Loan stacking — applying for multiple loans simultaneously from different lenders before any single lender can detect the others — often involves slight variations of a real email address. Gmail's plus-addressing feature ([email protected], [email protected]) and the fact that Gmail ignores dots in local parts ([email protected] = [email protected]) mean that a single Gmail account can generate dozens of technically distinct email addresses.
A sophisticated lending email verification system must normalize email addresses before storing them, stripping plus-tags and dots from known providers, to detect when the same underlying account is being used across multiple applications.
Account Takeover and Typosquatting
Account takeover (ATO) fraud in lending often begins when a fraudster gains access to a legitimate borrower's email account, then modifies loan details or initiates new applications. Separately, typosquatting — where applicants accidentally enter gnail.com instead of gmail.com — creates a different problem: the loan documents go nowhere, the borrower never receives their OTP, and your customer support queue fills up with "I never got my verification email" tickets.
According to HubSpot's 2023 Email Marketing Statistics Report, invalid email addresses account for between 2% and 8% of all form submissions across industries. In lending, where every application triggers downstream KYC processes, credit bureau pulls, and compliance workflows, even a 2% invalid rate represents significant operational waste.
The Technical Architecture of Email Verification: From Regex to SMTP
Most developers' first instinct is to validate email addresses with a regular expression. This is necessary but catastrophically insufficient. Let's walk through the full verification stack that a production lending platform should implement.
Layer 1 — Syntax Validation
Syntax validation checks whether an email address conforms to the format defined in RFC 5321 (Simple Mail Transfer Protocol) and RFC 5322 (Internet Message Format). RFC 5321 defines the envelope-level SMTP protocol, while RFC 5322 defines the message format including the From: header.
A syntactically valid email address must have:
- A local part (before the @) of maximum 64 characters
- A domain part (after the @) of maximum 255 characters
- No consecutive dots in the local part (unless quoted)
- Valid characters in both parts per RFC 5321 specifications
What regex cannot catch: whether the domain exists, whether the mailbox exists, whether the address is disposable, or whether the address has ever sent or received email.
Layer 2 — DNS Validation
After syntax validation, the next layer checks whether the domain has valid DNS records capable of receiving email. This means querying for MX (Mail Exchange) records. If a domain has no MX records, no mail server is configured to receive email for that domain, and the address is undeliverable by definition.
A production DNS validation check also examines:
- A records: If no MX record exists, some mail servers fall back to the A record. A valid A record can indicate deliverability in edge cases.
- SPF records (RFC 7208): The Sender Policy Framework defines which mail servers are authorized to send email on behalf of a domain. An SPF record looks like this:
v=spf1 include:_spf.google.com include:mailgun.org ~all
The presence and validity of an SPF record is a strong signal that a domain is actively managed and used for real email communication.
- DKIM records (RFC 6376): DomainKeys Identified Mail allows a domain to cryptographically sign outgoing messages. A DKIM TXT record at a selector subdomain looks like:
v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQC...
- DMARC records (RFC 7489): Domain-based Message Authentication, Reporting, and Conformance builds on SPF and DKIM. A DMARC record at
_dmarc.example.comlooks like:
v=DMARC1; p=reject; rua=mailto:[email protected]; ruf=mailto:[email protected]; pct=100
A domain with a p=reject DMARC policy is actively managed and monitored — a positive signal for legitimacy.
Layer 3 — SMTP Mailbox Verification
This is where real email verification diverges from simple checks. SMTP mailbox verification involves establishing a connection to the recipient domain's mail server and simulating the beginning of an email delivery — without actually sending a message. This is often called an SMTP handshake or MX record ping.
The process follows the SMTP protocol defined in RFC 5321:
- Connect to the MX server on port 25
- Send
EHLO(Extended Hello) - Send
MAIL FROM: <[email protected]> - Send
RCPT TO: <[email protected]> - Receive the server's response
- Send
QUITwithout completing the transaction
The response to the RCPT TO command tells you definitively whether the mailbox exists:
- 250: Success — the mailbox exists and can receive mail
- 550: Mailbox not found / does not exist (most common rejection for invalid addresses)
- 551: User not local; please try forwarding — the address may exist elsewhere
- 552: Exceeded storage allocation — the mailbox exists but is full
- 421: Service not available, closing transmission channel — temporary issue, retry later
- 450: Requested mail action not taken — temporary failure, often a greylisting response
These response codes are defined in RFC 3463 (Enhanced Mail System Status Codes), which provides extended status codes in the format X.Y.Z that give more granular information than the basic three-digit codes.
Layer 4 — Behavioral and Risk Signals
Beyond the technical verification layers, a production fintech fraud prevention system enriches email verification with risk signals:
- Domain age: Newly registered domains (less than 30 days old) are high-risk
- Disposable email detection: Matching against known disposable provider domains and infrastructure
- Free vs. corporate email: A loan application from
[email protected]carries different risk than one from[email protected] - Breach data: Has this email appeared in known data breaches? (Relevant for ATO risk)
- Email activity signals: Does this address have a sending history? Is it associated with social accounts?
- Catch-all detection: Some domains are configured to accept mail for any local part, making SMTP verification inconclusive
Mapping Email Verification to KYC Compliance Frameworks
KYC compliance in lending is governed by a layered regulatory framework. In the United States, the primary requirements come from:
- Bank Secrecy Act (BSA) and its implementing regulations
- FinCEN's Customer Due Diligence (CDD) Rule (31 CFR § 1020.210)
- USA PATRIOT Act Section 326 — Customer Identification Program (CIP) requirements
- CFPB's fair lending and UDAAP regulations
- State-level money transmitter and lending laws
For platforms operating internationally, FATF Recommendations, EU's 5th Anti-Money Laundering Directive (5AMLD), and PSD2 create additional obligations.
Where Email Verification Fits in the CDD Rule
FinCEN's CDD Rule requires covered financial institutions to collect and verify identifying information for customers. The four core elements are: name, date of birth, address, and identification number. Email address is not explicitly listed — but this is where many compliance officers stop thinking about it, and that's a mistake.
Email verification supports KYC compliance in three critical ways:
First, it validates the authenticity of the customer contact point. A KYC process that verifies a government ID but delivers all subsequent communications to a disposable email address has a fundamental integrity gap. If you can't reliably reach the customer, you can't fulfill ongoing due diligence obligations.
Second, email verification is a component of the "reasonable procedures" standard. FinCEN's guidance consistently emphasizes that institutions must implement procedures reasonably designed to achieve compliance. Accepting unverified email addresses when verification technology is readily available and inexpensive is increasingly difficult to defend as "reasonable."
Third, email verification supports Enhanced Due Diligence (EDD) triggers. When email verification returns high-risk signals — disposable domain, newly registered domain, SMTP rejection — these should automatically trigger EDD workflows: additional document requests, manual review, or application rejection.
Email Verification and GDPR/CCPA Considerations
An important compliance nuance: in jurisdictions covered by GDPR (EU/EEA) or CCPA (California), the act of performing SMTP verification on a user's email address may constitute processing of personal data. Your privacy policy and terms of service should disclose that email addresses are verified as part of your identity verification process. MailValid.io's API is designed to minimize data retention during verification, returning results without storing the verified address beyond the transaction window.
Production Implementation: Integrating Email Verification into Your Lending Platform
Theory is useful. Production code is what matters. Here's how to integrate email verification into a lending platform's application flow, with real error handling and compliance-appropriate logic.
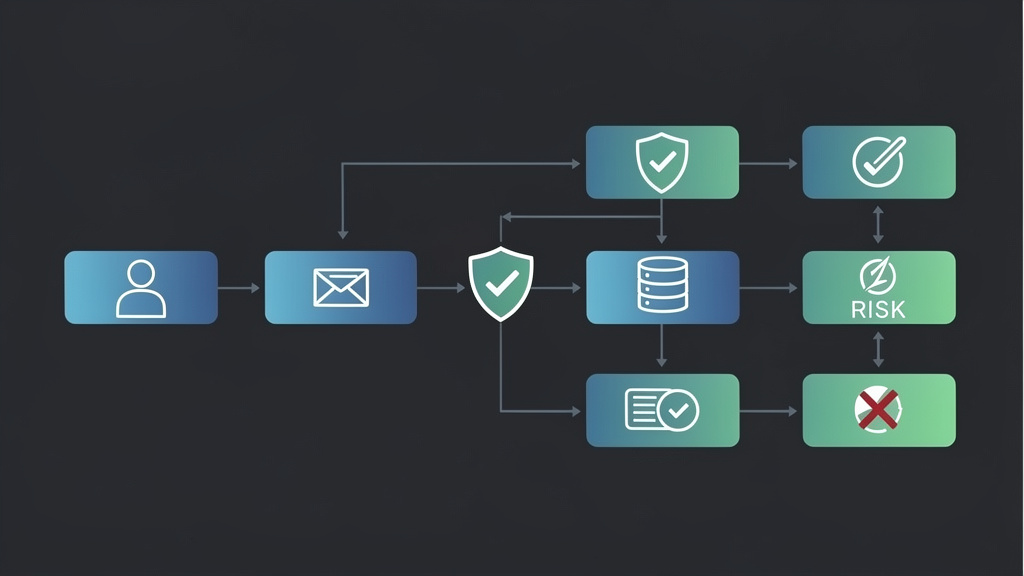
Integration Architecture
The recommended architecture for lending email verification places the API call at two points in the application flow:
- Real-time, at form submission: Provide immediate feedback to legitimate applicants (catches typos) while flagging high-risk addresses before any downstream processes are triggered.
- Batch processing, for existing pipelines: If you're integrating into an existing system with a backlog of unverified addresses, a batch verification pass cleans your database and improves deliverability for ongoing communications.
Python Implementation with MailValid API
The following is a production-ready implementation for a FastAPI-based lending platform backend. It includes proper error handling, risk-based routing, and compliance logging.
import requests
import logging
import hashlib
from enum import Enum
from typing import Optional, Dict, Any
from datetime import datetime
# Configure structured logging for compliance audit trail
logging.basicConfig(
level=logging.INFO,
format='%(asctime)s %(levelname)s %(name)s %(message)s'
)
logger = logging.getLogger("email_verification")
class EmailRiskLevel(Enum):
VERIFIED = "verified"
SUSPICIOUS = "suspicious"
HIGH_RISK = "high_risk"
REJECTED = "rejected"
class EmailVerificationResult:
def __init__(self, raw_result: Dict[str, Any], email: str):
self.email = email
self.email_hash = hashlib.sha256(email.lower().encode()).hexdigest()
self.is_valid = raw_result.get("valid", False)
self.is_deliverable = raw_result.get("deliverable", False)
self.is_disposable = raw_result.get("disposable", False)
self.is_catch_all = raw_result.get("catch_all", False)
self.is_role_based = raw_result.get("role_based", False)
self.smtp_code = raw_result.get("smtp_code")
self.domain_age_days = raw_result.get("domain_age_days")
self.mx_found = raw_result.get("mx_found", False)
self.spf_valid = raw_result.get("spf_valid", False)
self.dmarc_valid = raw_result.get("dmarc_valid", False)
self.risk_score = raw_result.get("risk_score", 100)
self.provider = raw_result.get("provider", "unknown")
self.verified_at = datetime.utcnow().isoformat()
def get_risk_level(self) -> EmailRiskLevel:
"""
Map verification results to lending-specific risk levels.
Thresholds should be calibrated to your fraud tolerance.
"""
if not self.is_valid or not self.mx_found:
return EmailRiskLevel.REJECTED
if self.is_disposable:
return EmailRiskLevel.REJECTED
if self.smtp_code in [550, 551]:
return EmailRiskLevel.REJECTED
if (
self.domain_age_days is not None and self.domain_age_days < 30
) or self.risk_score > 75:
return EmailRiskLevel.HIGH_RISK
if (
self.is_catch_all
or self.is_role_based
or self.smtp_code in [450, 421]
or self.risk_score > 40
):
return EmailRiskLevel.SUSPICIOUS
return EmailRiskLevel.VERIFIED
def to_compliance_log(self) -> Dict[str, Any]:
"""
Return a compliance-safe log entry.
Note: stores hash, not plaintext email, for GDPR compliance.
"""
return {
"email_hash": self.email_hash,
"risk_level": self.get_risk_level().value,
"is_deliverable": self.is_deliverable,
"is_disposable": self.is_disposable,
"smtp_code": self.smtp_code,
"risk_score": self.risk_score,
"mx_found": self.mx_found,
"spf_valid": self.spf_valid,
"dmarc_valid": self.dmarc_valid,
"domain_age_days": self.domain_age_days,
"provider": self.provider,
"verified_at": self.verified_at,
}
def verify_email_for_lending(
email: str,
api_key: str = "mv_live_key",
timeout: int = 10,
retry_on_temp_failure: bool = True
) -> Optional[EmailVerificationResult]:
"""
Verify an email address using the MailValid API.
Args:
email: The email address to verify
api_key: Your MailValid API key
timeout: Request timeout in seconds
retry_on_temp_failure: Retry on 450/421 SMTP responses
Returns:
EmailVerificationResult or None if API is unavailable
"""
url = "https://mailvalid.io/api/v1/verify"
headers = {"X-API-Key": api_key}
payload = {"email": email}
try:
response = requests.post(
url,
headers=headers,
json=payload,
timeout=timeout
)
result = response.json()
# Handle API-level errors
if response.status_code == 401:
logger.error("MailValid API authentication failed. Check API key.")
raise ValueError("Invalid API key")
if response.status_code == 429:
logger.warning("MailValid API rate limit reached. Implement backoff.")
raise RuntimeError("Rate limit exceeded")
if response.status_code not in [200, 201]:
logger.error(
f"MailValid API returned unexpected status: {response.status_code}"
)
return None
verification = EmailVerificationResult(result, email)
risk_level = verification.get_risk_level()
# Log for compliance audit trail (hash only, not plaintext)
logger.info(
"email_verification_complete",
extra={
"audit": verification.to_compliance_log()
}
)
# Trigger EDD workflow for high-risk results
if risk_level in [EmailRiskLevel.HIGH_RISK, EmailRiskLevel.SUSPICIOUS]:
logger.warning(
f"High-risk email detected. Risk level: {risk_level.value}. "
f"SMTP code: {verification.smtp_code}. "
f"Triggering EDD workflow."
)
return verification
except requests.exceptions.Timeout:
logger.error(
"MailValid API timeout. Consider fail-open with manual review flag."
)
# In lending, fail-open with a manual review flag is safer than fail-closed
# which would block legitimate applicants. Adjust based on your risk appetite.
return None
except requests.exceptions.ConnectionError:
logger.error("Cannot reach MailValid API. Check network connectivity.")
return None
except Exception as e:
logger.error(f"Unexpected error during email verification: {str(e)}")
return None
def process_loan_application_email(
email: str,
application_id: str,
api_key: str
) -> Dict[str, Any]:
"""
Process email verification as part of a loan application flow.
Returns a decision dict with action and reason.
"""
result = verify_email_for_lending(email, api_key)
if result is None:
# API unavailable — flag for manual review, do not auto-reject
return {
"action": "manual_review",
"reason": "email_verification_service_unavailable",
"application_id": application_id,
"edd_required": True
}
risk_level = result.get_risk_level()
decision_map = {
EmailRiskLevel.VERIFIED: {
"action": "proceed",
"reason": "email_verified",
"edd_required": False
},
EmailRiskLevel.SUSPICIOUS: {
"action": "proceed_with_edd",
"reason": f"email_suspicious_smtp_{result.smtp_code}",
"edd_required": True
},
EmailRiskLevel.HIGH_RISK: {
"action": "manual_review",
"reason": "email_high_risk_signals",
"edd_required": True
},
EmailRiskLevel.REJECTED: {
"action": "reject",
"reason": f"email_invalid_or_disposable_smtp_{result.smtp_code}",
"edd_required": False
}
}
decision = decision_map[risk_level].copy()
decision["application_id"] = application_id
decision["email_hash"] = result.email_hash
decision["risk_score"] = result.risk_score
return decision
# Example usage in a loan application handler
if __name__ == "__main__":
API_KEY = "mv_live_key"
test_cases = [
("[email protected]", "APP-001"),
("[email protected]", "APP-002"),
("[email protected]", "APP-003"),
("[email protected]", "APP-004"),
]
for email, app_id in test_cases:
decision = process_loan_application_email(email, app_id, API_KEY)
print(f"Application {app_id}: {decision['action']} — {decision['reason']}")
JavaScript / Node.js Implementation
For teams running Node.js backends — common in fintech startups using Express or NestJS — here's an equivalent production implementation:
const axios = require('axios');
const crypto = require('crypto');
const EmailRiskLevel = {
VERIFIED: 'verified',
SUSPICIOUS: 'suspicious',
HIGH_RISK: 'high_risk',
REJECTED: 'rejected'
};
const TEMP_SMTP_CODES = [421, 450];
const REJECTION_SMTP_CODES = [550, 551];
/**
* Hash email for GDPR-compliant logging
*/
function hashEmail(email) {
return crypto
.createHash('sha256')
.update(email.toLowerCase())
.digest('hex');
}
/**
* Determine risk level from MailValid API response
*/
function getRiskLevel(result) {
if (!result.valid || !result.mx_found) return EmailRiskLevel.REJECTED;
if (result.disposable) return EmailRiskLevel.REJECTED;
if (REJECTION_SMTP_CODES.includes(result.smtp_code)) return EmailRiskLevel.REJECTED;
if (
(result.domain_age_days !== null && result.domain_age_days < 30) ||
result.risk_score > 75
) {
return EmailRiskLevel.HIGH_RISK;
}
if (
result.catch_all ||
result.role_based ||
TEMP_SMTP_CODES.includes(result.smtp_code) ||
result.risk_score > 40
) {
return EmailRiskLevel.SUSPICIOUS;
}
return EmailRiskLevel.VERIFIED;
}
/**
* Verify email using MailValid API
* @param {string} email - Email address to verify
* @param {string} apiKey - MailValid API key
* @returns {Promise<Object>} Verification result with risk assessment
*/
async function verifyEmailForLending(email, apiKey) {
try {
const response = await axios.post(
'https://mailvalid.io/api/v1/verify',
{ email },
{
headers: { 'X-API-Key': apiKey },
timeout: 10000 // 10 second timeout
}
);
const result = response.data;
const riskLevel = getRiskLevel(result);
const emailHash = hashEmail(email);
// Structured compliance log (no plaintext PII)
const complianceLog = {
email_hash: emailHash,
risk_level: riskLevel,
is_deliverable: result.deliverable,
is_disposable: result.disposable,
smtp_code: result.smtp_code,
risk_score: result.risk_score,
mx_found: result.mx_found,
spf_valid: result.spf_valid,
dmarc_valid: result.dmarc_valid,
domain_age_days: result.domain_age_days,
provider: result.provider,
verified_at: new Date().toISOString()
};
console.log(JSON.stringify({ level: 'info', event: 'email_verified', ...complianceLog }));
return {
riskLevel,
emailHash,
smtpCode: result.smtp_code,
riskScore: result.risk_score,
isDisposable: result.disposable,
isCatchAll: result.catch_all,
provider: result.provider,
complianceLog
};
} catch (error) {
if (error.response?.status === 401) {
throw new Error('MailValid API authentication failed');
}
if (error.response?.status === 429) {
console.warn(JSON.stringify({ level: 'warn', event: 'rate_limit_reached' }));
throw new Error('Rate limit exceeded — implement exponential backoff');
}
if (error.code === 'ECONNABORTED') {
console.error(JSON.stringify({ level: 'error', event: 'api_timeout' }));
return null; // Fail-open with manual review flag
}
console.error(JSON.stringify({ level: 'error', event: 'verification_error', message: error.message }));
return null;
}
}
/**
* Route loan application based on email verification result
*/
async function processLoanApplicationEmail(email, applicationId, apiKey) {
const verification = await verifyEmailForLending(email, apiKey);
if (!verification) {
return {
action: 'manual_review',
reason: 'email_verification_unavailable',
applicationId,
eddRequired: true
};
}
const decisions = {
[EmailRiskLevel.VERIFIED]: {
action: 'proceed',
reason: 'email_verified',
eddRequired: false
},
[EmailRiskLevel.SUSPICIOUS]: {
action: 'proceed_with_edd',
reason: `email_suspicious_smtp_${verification.smtpCode}`,
eddRequired: true
},
[EmailRiskLevel.HIGH_RISK]: {
action: 'manual_review',
reason: 'email_high_risk_signals',
eddRequired: true
},
[EmailRiskLevel.REJECTED]: {
action: 'reject',
reason: `email_invalid_or_disposable_smtp_${verification.smtpCode}`,
eddRequired: false
}
};
return {
...decisions[verification.riskLevel],
applicationId,
emailHash: verification.emailHash,
riskScore: verification.riskScore
};
}
module.exports = { verifyEmailForLending, processLoanApplicationEmail, EmailRiskLevel };
Common Mistakes Lending Platforms Make with Email Verification
Understanding what not to do is as important as knowing the right approach. These are the most common failures we see in production lending systems.
Mistake 1 — Treating Regex as Sufficient Validation
A regular expression can confirm that an email address looks syntactically valid. It cannot confirm that the domain accepts mail, that the mailbox exists, or that the address isn't disposable. A regex check will happily pass [email protected] and reject nothing. This is the most pervasive mistake in the industry.
Mistake 2 — Blocking All Free Email Providers
The overcorrection to disposable email detection is blocking all free email providers — Gmail, Yahoo, Outlook, etc. This is a significant business mistake. According to Litmus's 2023 Email Client Market Share Report, Gmail alone accounts for approximately 29% of all email opens globally. A large proportion of legitimate borrowers, particularly younger demographics and gig economy workers, use Gmail as their primary email. Blocking free providers will reject legitimate applicants and create fair lending exposure if the policy has a disparate impact on protected classes.
The correct approach is risk-scoring free providers rather than blocking them outright. A verified, non-disposable Gmail address with a risk score below your threshold should proceed normally.
Mistake 3 — Performing Verification Only at Signup
Email addresses change. Borrowers change jobs and lose corporate email accounts. Free email providers occasionally shut down domains. A verification that was valid at application time may become invalid 18 months later when you need to send a collections notice or a regulatory disclosure. Implement periodic re-verification for active borrower accounts, particularly before sending legally required communications.
Mistake 4 — Ignoring Catch-All Domains
A catch-all domain is configured to accept SMTP connections for any local part — meaning RCPT TO: <[email protected]> will return a 250 success code even if the specific mailbox doesn't exist. An SMTP verification against a catch-all domain cannot confirm whether the specific address is real. Your verification system must detect catch-all configurations and flag them appropriately — typically routing them to a confirmation email flow rather than treating them as fully verified.
Mistake 5 — No Fail-Safe Strategy
What happens when your email verification API is unavailable? If your answer is "we block all applications," you've created a single point of failure that fraudsters can potentially exploit (by triggering API outages) and that will certainly frustrate legitimate applicants during real outages. The recommended pattern is fail-open with enhanced scrutiny: allow the application to proceed but flag it for manual review and require additional verification steps.
Mistake 6 — Not Normalizing Email Addresses Before Storage
As discussed in the loan stacking section, email address normalization is essential for deduplication. Before storing any email address, apply these normalizations:
- Convert to lowercase
- For Gmail addresses: remove dots from local part, remove plus-tags
- For Outlook/Hotmail addresses: remove plus-tags
- Store the normalized form alongside the original for display purposes
This prevents the same Gmail account from appearing as multiple distinct applicants in your database.
Email Verification and Anti-Money Laundering: The Overlooked Connection
The connection between email verification and anti-money laundering (AML) compliance is less obvious than the KYC connection, but it's equally important for lending platforms.
Structuring Detection and Email Patterns
AML regulations require lenders to monitor for structuring — breaking up transactions to avoid reporting thresholds. In digital lending, structuring often involves multiple accounts created with slight email variations. A robust email normalization and deduplication system that's part of your verification infrastructure directly supports structuring detection by identifying when multiple accounts trace back to the same underlying email identity.
Beneficial Ownership and Email Verification
For business lending, FinCEN's Beneficial Ownership Rule requires identifying and verifying the identity of individuals who own or control legal entity customers. Email addresses for beneficial owners should be subject to the same verification standards as individual borrowers. A beneficial owner who provides a disposable email address is a significant red flag that should trigger EDD.
Suspicious Activity Reports (SARs) and Email Evidence
When a lending platform files a SAR with FinCEN, the quality of the digital identity evidence — including email verification records — affects the utility of that report for law enforcement. Maintaining detailed, timestamped email verification audit logs (with hashed email addresses for privacy compliance) creates a defensible evidentiary record.
Benchmarking Email Verification Performance: What Good Looks Like
How do you know if your email verification implementation is performing well? Here are the key metrics lending platforms should track, with industry benchmarks.
Application-Level Metrics
- Invalid email rate at submission: Industry average is 2-8% across all verticals. For lending platforms with verification in place, this should drop to under 1% within 90 days of implementation.
- Disposable email detection rate: If you're not catching at least 3-5% of applications as disposable, your detection database may be outdated. The disposable email ecosystem adds new domains constantly.
- Verification API response time: For real-time form validation, your P95 response time should be under 3 seconds. MailValid's API targets sub-1-second P95 response times for most domains.
- Catch-all detection rate: Expect 5-15% of business email domains to be catch-all configured. These require the confirmation email flow.
Fraud and Compliance Metrics
- Fraud rate correlation: Track the fraud rate (chargebacks, defaults linked to fraud) for applications that passed vs. flagged email verification. A well-calibrated system should show 3-5x higher fraud rates in the flagged cohort.
- EDD trigger rate: Your email verification should trigger EDD for approximately 8-15% of applications. If it's triggering for fewer than 5%, your thresholds may be too permissive. If it's triggering for more than 25%, you're likely creating unnecessary friction for legitimate borrowers.
- False positive rate: Monitor how many manually reviewed applications that were flagged by email verification ultimately prove to be legitimate. A false positive rate above 20% indicates over-aggressive thresholds.
Deliverability Metrics
Email verification isn't just about fraud prevention — it directly improves the deliverability of your ongoing borrower communications. According to Return Path's (now Validity's) Benchmark Report, sender reputation scores above 90 correlate with inbox placement rates above 95%. Every invalid address you prevent from entering your system is a potential bounce you prevent from damaging your sender reputation.
Track these deliverability metrics monthly: - Hard bounce rate: Should be under 2% per send. Above 5% triggers spam filter penalties. - Soft bounce rate: Should be under 5%. High soft bounce rates indicate catch-all domains or full mailboxes. - Spam complaint rate: Should be under 0.1%. Relevant if borrowers mark your loan communications as spam due to address confusion.
Best Practices for Email Verification in Regulated Lending Environments
Bringing together everything covered in this post, here are the actionable best practices for implementing lending email verification that satisfies both technical and KYC compliance requirements.
Build a Layered Verification Pipeline
Don't rely on a single verification signal. Implement all four layers: syntax validation, DNS/MX validation, SMTP mailbox verification, and behavioral risk scoring. Each layer catches different fraud vectors. A sophisticated fraudster can pass layers one through three with a real-but-abandoned email address — behavioral risk scoring is what catches them.
Implement Verification at Multiple Application Touchpoints
- Pre-submit (client-side): Syntax check and domain validation for immediate typo feedback
- On-submit (server-side): Full SMTP verification and risk scoring before the application enters your pipeline
- Pre-communication (batch): Re-verify before sending legally required disclosures, statements, or collections communications
- Periodic (scheduled): Quarterly re-verification of active borrower email addresses
Create a Risk-Tiered Response System
Don't make email verification binary (pass/fail). Implement the four-tier system demonstrated in the code examples above: Verified, Suspicious, High-Risk, and Rejected. This allows you to preserve revenue from borderline-risk applicants through enhanced due diligence rather than outright rejection, while still protecting against clear fraud.
Maintain Compliance-Grade Audit Logs
Every email verification event should be logged with: - Timestamp (UTC) - Hashed email address (SHA-256, not plaintext — GDPR compliance) - Verification outcome and risk level - SMTP response code - Key risk signals (disposable, catch-all, domain age) - Application or account identifier - Verification service version/provider
These logs are your evidence in regulatory examinations and fraud disputes.
Integrate with Your Broader Fraud Stack
Email verification is one signal among many. Integrate it with your device fingerprinting, IP reputation, velocity checks, and identity verification systems. A risk orchestration layer that combines these signals — rather than evaluating each in isolation — produces significantly better fraud detection with lower false positive rates.
Stay Current on Disposable Email Domains
The disposable email ecosystem is dynamic. New providers emerge constantly, and some operate under legitimate-looking domains specifically to evade detection. Ensure your verification provider maintains a continuously updated disposable domain database. MailValid.io updates its disposable domain detection in real time, covering thousands of known temporary email providers and their infrastructure.
Test Your Verification Logic Regularly
Implement automated tests that send known-bad email types through your verification pipeline: - Known disposable domains (Mailinator, 10MinuteMail, etc.) - Syntactically invalid addresses - Non-existent domains - Real domains with non-existent mailboxes - Catch-all domains
Run these tests in your CI/CD pipeline to catch regressions before they reach production.
Conclusion: Email Verification Is Non-Negotiable for Lending Compliance
The lending industry operates at the intersection of consumer trust, regulatory obligation, and sophisticated adversarial fraud. Every loan application that enters your pipeline with an unverified email address is a potential fraud vector, a compliance gap, and an operational liability.
Lending email verification is not a nice-to-have feature — it's a foundational component of a defensible KYC compliance program. The technical infrastructure exists, the regulatory imperative is clear, and the cost of implementation is trivial compared to the cost of a single synthetic identity fraud case. A well-implemented verification system, built on SMTP-level validation per RFC 5321, enriched with DNS authentication signals from RFC 7208 (SPF), RFC 6376 (DKIM), and RFC 7489 (DMARC), and integrated with behavioral risk scoring, can detect the vast majority of fraudulent email addresses before they ever enter your application pipeline.
The code examples in this post give you a production-ready starting point. The compliance framework maps your technical implementation to regulatory requirements. The benchmarks give you targets to measure against.
Fintech fraud prevention starts with the simplest piece of data on your application form. Don't let it be your weakest link.
[!TIP]
Verify Every Email. Protect Every Loan. MailValid.io provides enterprise-grade email verification built for the compliance requirements of lending platforms, fintechs, and regulated financial services. Our API delivers SMTP-level mailbox verification, real-time disposable domain detection, DNS authentication analysis, and risk scoring — all in a single API call with sub-second response times. Start verifying in minutes: - Free tier available — 1,000 verifications/month at no cost - SOC 2 Type II compliant infrastructure - GDPR-ready — minimal data retention, EU data residency options - 99.9% uptime SLA — because your application pipeline can't afford downtime - Dedicated support for compliance and integration questions Get Your Free API Key → | View API Documentation → | Talk to a Compliance Expert → Trusted by lending platforms processing millions of applications annually. Integrate in under an hour.
MailValid Team
Email verification experts
Join developers who verify smarter
Stop letting bad emails hurt your deliverability
100 free credits. $0.001/email after. Credits never expire. No credit card required.